23-11
Catalyst 2960 and 2960-S Switch Software Configuration Guide
OL-8603-09
Chapter 23 Configuring Port-Based Traffic Control
Configuring Port Security
Default Port Security Configuration
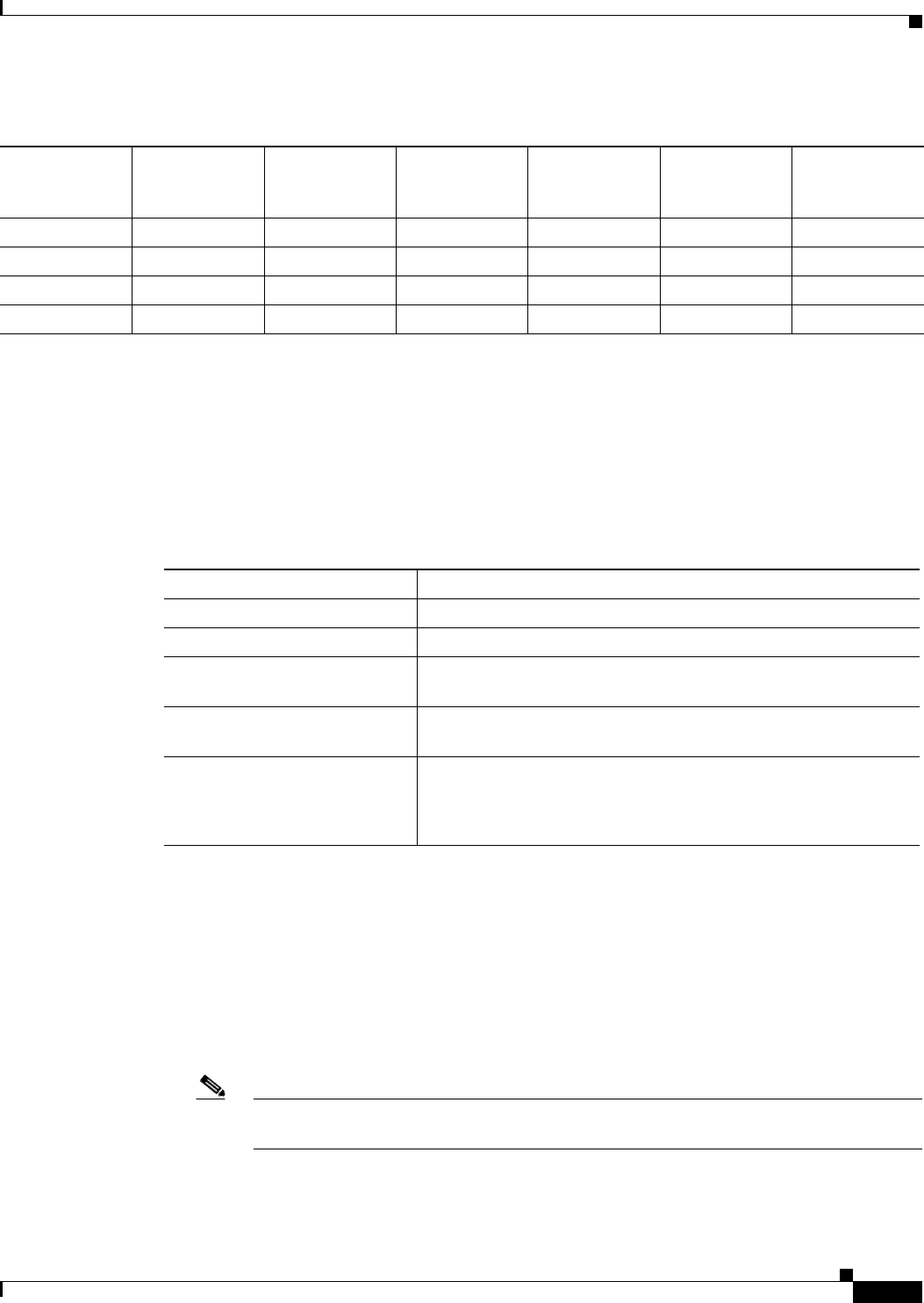
Table 23-2 shows the default port security configuration for an interface.
Port Security Configuration Guidelines
Follow these guidelines when configuring port security:
• Port security can only be configured on static access ports or trunk ports. A secure port cannot be a
dynamic access port.
• A secure port cannot be a destination port for Switched Port Analyzer (SPAN).
• A secure port cannot belong to a Fast EtherChannel or a Gigabit EtherChannel port group.
Note Voice VLAN is only supported on access ports and not on trunk ports, even though the
configuration is allowed.
Table 23-1 Security Violation Mode Actions
Violation Mode
Traffic is
forwarded
1
1. Packets with unknown source addresses are dropped until you remove a sufficient number of secure MAC addresses.
Sends SNMP
trap
Sends syslog
message
Displays error
message
2
2. The switch returns an error message if you manually configure an address that would cause a security violation.
Violation
counter
increments Shuts down port
protect No No No No No No
restrict No Yes Yes No Yes No
shutdown No No No No Yes Yes
shutdown vlan No No Yes No Yes No
3
3. Shuts down only the VLAN on which the violation occurred.
Table 23-2 Default Port Security Configuration
Feature Default Setting
Port security Disabled on a port.
Sticky address learning Disabled.
Maximum number of secure
MAC addresses per port
1
Violation mode Shutdown. The port shuts down when the maximum number of
secure MAC addresses is exceeded.
Port security aging Disabled. Aging time is 0.
Static aging is disabled.
Type is absolute.


















