10-58
Catalyst 2960 and 2960-S Switch Software Configuration Guide
OL-8603-09
Chapter 10 Configuring IEEE 802.1x Port-Based Authentication
Configuring 802.1x Authentication
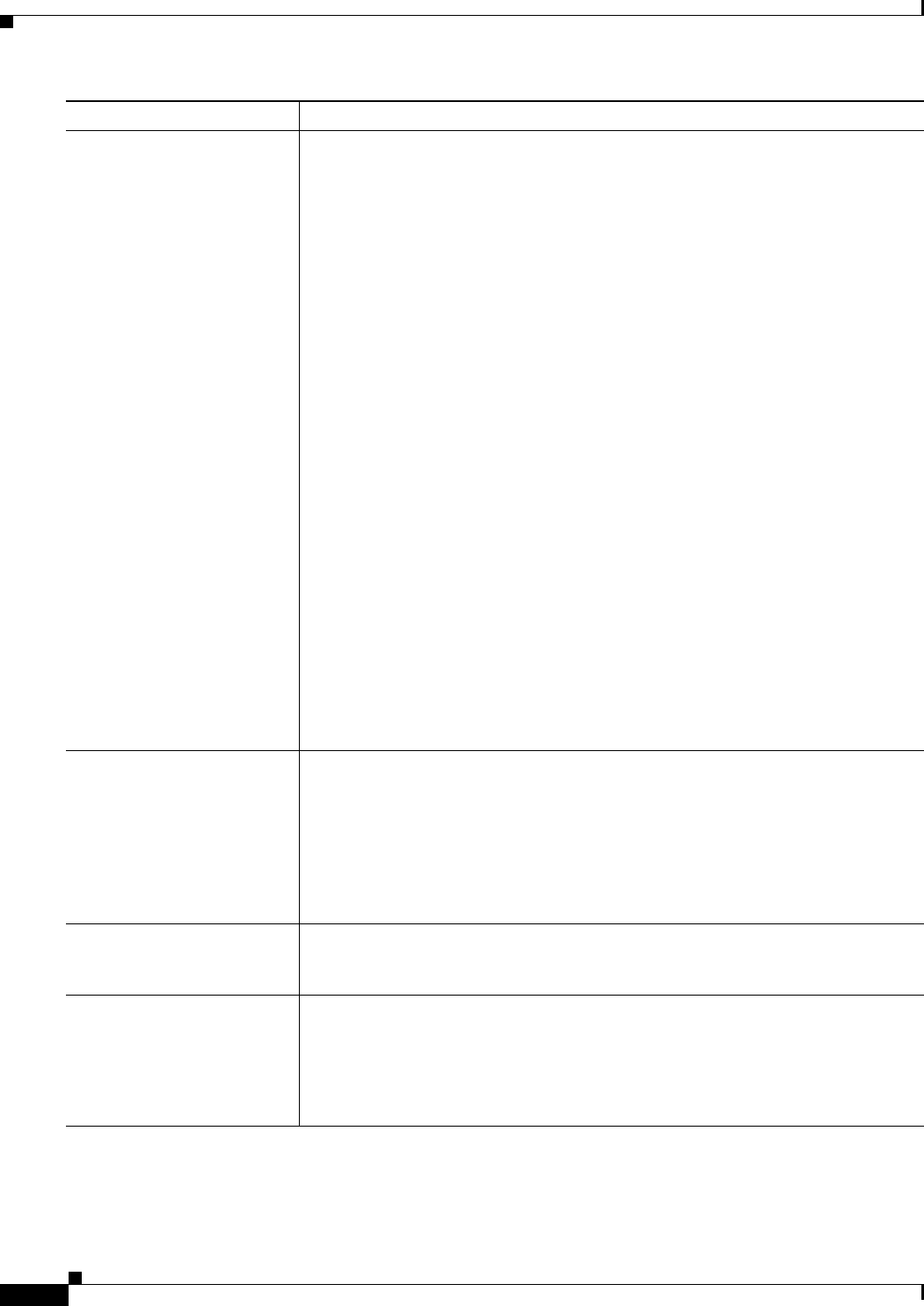
Step 4
radius-server host
ip-address [acct-port
udp-port] [auth-port
udp-port] [test username
name [idle-time time]
[ignore-acct-port]
[ignore-auth-port]] [key
string]
(Optional) Configure the RADIUS server parameters by using these keywords:
• acct-port udp-port—Specify the UDP port for the RADIUS accounting server.
The range for the UDP port number is from 0 to 65536. The default is 1646.
• auth-port udp-port—Specify the UDP port for the RADIUS authentication
server. The range for the UDP port number is from 0 to 65536. The default is
1645.
Note You should configure the UDP port for the RADIUS accounting server and
the UDP port for the RADIUS authentication server to nondefault values.
• test username name—Enable automated testing of the RADIUS server status,
and specify the username to be used.
• idle-time time—Set the interval of time in minutes after which the switch sends
test packets to the server. The range is from 1 to 35791 minutes. The default is
60 minutes (1 hour).
• ignore-acct-port—Disable testing on the RADIUS-server accounting port.
• ignore-auth-port—Disable testing on the RADIUS-server authentication port.
• key string—Specify the authentication and encryption key for all RADIUS
communication between the switch and the RADIUS daemon.
Note Always configure the key as the last item in the radius-server host
command syntax because leading spaces are ignored, but spaces within and
at the end of the key are used. If you use spaces in the key, do not enclose
the key in quotation marks unless the quotation marks are part of the key.
This key must match the encryption used on the RADIUS daemon.
You can also configure the authentication and encryption key by using the
radius-server key {0 string | 7 string | string} global configuration command.
Step 5
dot1x critical {eapol |
recovery delay milliseconds}
(Optional) Configure the parameters for inaccessible authentication bypass:
eapol—Specify that the switch sends an EAPOL-Success message when the switch
successfully authenticates the critical port.
recovery delay milliseconds—Set the recovery delay period during which the
switch waits to re-initialize a critical port when a RADIUS server that was
unavailable becomes available. The range is from 1 to 10000 milliseconds. The
default is 1000 milliseconds (a port can be re-initialized every second).
Step 6
interface interface-id Specify the port to be configured, and enter interface configuration mode. For the
supported port types, see the “802.1x Authentication Configuration Guidelines”
section on page 10-38.
Step 7
authentication event server
dead action [authorize |
reinitialize] vlan vlan-id
Use these keywords to move hosts on the port if the RADIUS server is unreachable:
• authorize–Move any new hosts trying to authenticate to the user-specified
critical VLAN.
• reinitialize–Move all authorized hosts on the port to the user-specified critical
VLAN.
Command Purpose


















