10-43
Catalyst 2960 and 2960-S Switch Software Configuration Guide
OL-8603-09
Chapter 10 Configuring IEEE 802.1x Port-Based Authentication
Configuring 802.1x Authentication
Configuring 802.1x Violation Modes
Note To configure violation modes, the switch must be running the LAN base image.
You can configure an 802.1x port so that it shuts down, generates a syslog error, or discards packets from
a new device when:
• a device connects to an 802.1x-enabled port
• the maximum number of allowed about devices have been authenticated on the port
Beginning in privileged EXEC mode, follow these steps to configure the security violation actions on
the switch:
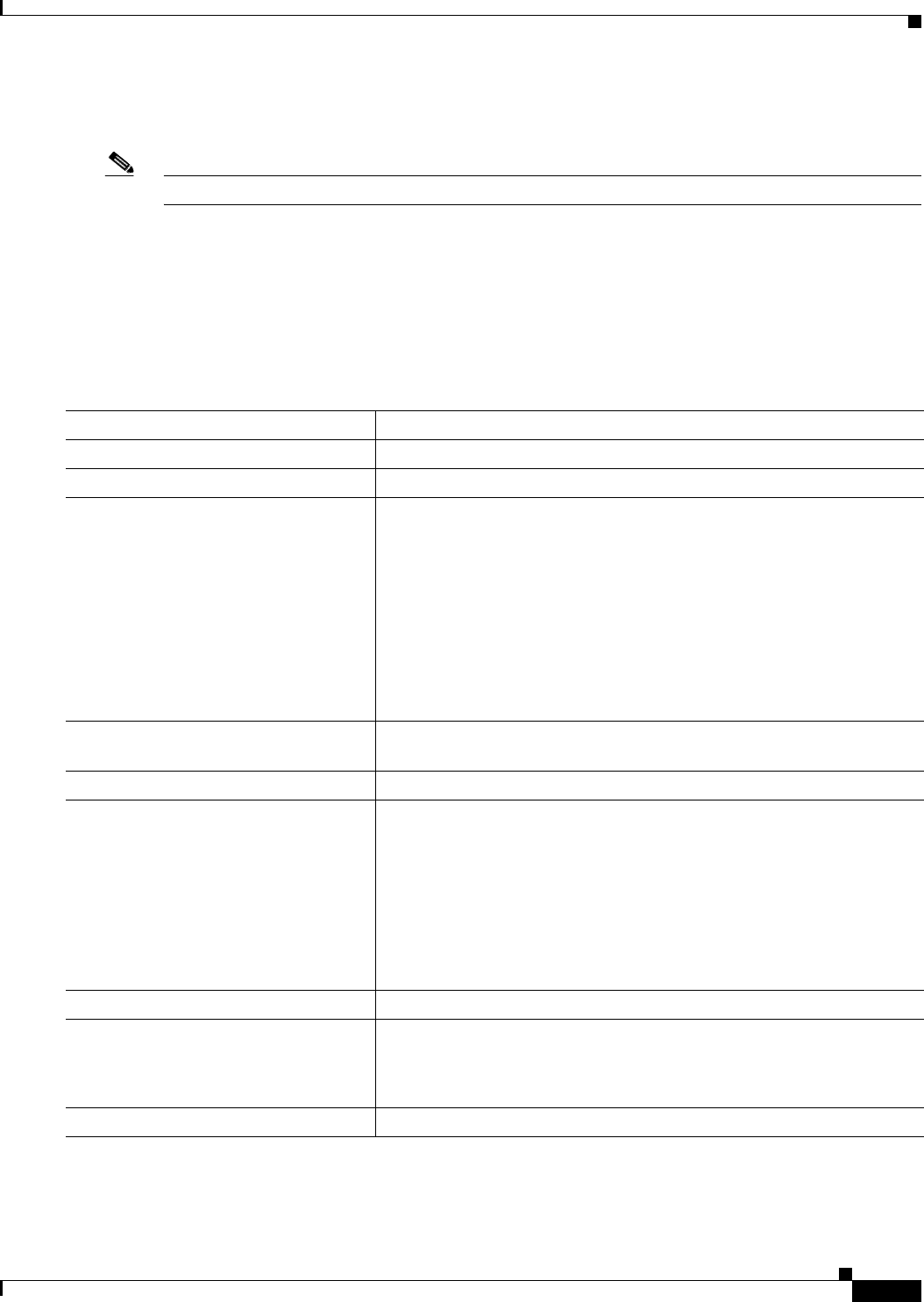
Command Purpose
Step 1
configure terminal Enter global configuration mode.
Step 2
aaa new-model Enable AAA.
Step 3
aaa authentication dot1x {default}
method1
Create an 802.1x authentication method list.
To create a default list to use when a named list is not specified in the
authentication command, use the default keyword followed by the
method that is to be used in default situations. The default method list is
automatically applied to all ports.
For method1, enter the group radius keywords to use the list of all
RADIUS servers for authentication.
Note Though other keywords are visible in the command-line help
string, only the group radius keywords are supported.
Step 4
interface interface-id Specify the port connected to the client that is to be enabled for 802.1x
authentication, and enter interface configuration mode.
Step 5
switchport mode access Set the port to access mode.
Step 6
authentication violation shutdown |
restrict | protect | replace}
or
dot1x violation-mode {shutdown |
restrict | protect}
Configure the violation mode. The keywords have these meanings:
• shutdown–Error disable the port.
• restrict–Generate a syslog error.
• protect–Drop packets from any new device that sends traffic to the
port.
• replace–Removes the current session and authenticates with the new
host.
Step 7
end Return to privileged EXEC mode.
Step 8
show authentication
or
show dot1x
Verify your entries.
Step 9
copy running-config startup-config (Optional) Save your entries in the configuration file.


















